Cyber threats are no longer theoretical. Nation-state actors, ransomware cartels, and insider threats are actively targeting U.S. government systems and cleared defense contractors every single day.
We specialize in securing federal information systems, safeguarding Controlled Unclassified Information (CUI), and guiding defense contractors through complex authorization frameworks — including RMF, CMMC, NIST 800-171, HIPAA, and DCSA requirements.
✔️ Dozens of cleared defense contractors authorized
✔️ Zero failed assessments
✔️ Proven track record sustaining compliant security programs
✔️ Trusted partner to mission-critical environments
Ransomware attacks have become a common practice by cybercriminals, exploiting the fact that most entities or users do not possess a comprehensive backup of their valuable data. These attacks encrypt information and demand a ransom in the form of bitcoin or other cryptocurrencies to release the decryption key

The most crucial component in establishing military-grade cybersecurity, is to start with a system baseline that provides the most restrictive environment without compromising system performance or functionality.
At PC-WARRIORS we have mastered this crucial component with our proprietary tools, resulting in military-grade cybersecurity without loss of system performance or functionality.
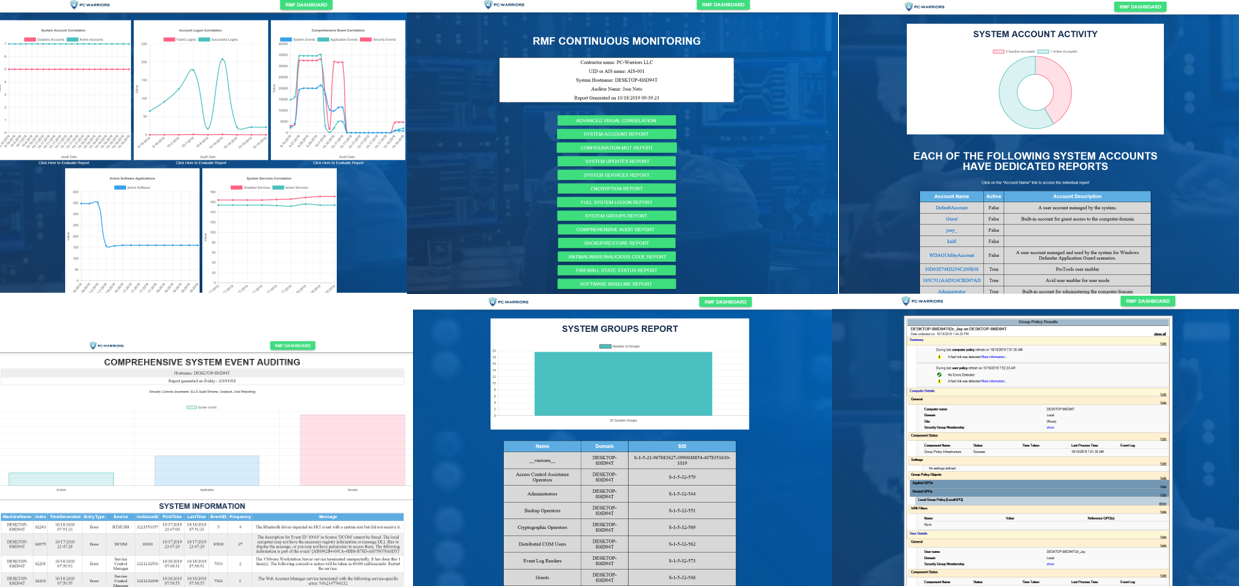
Our RMF-DASHBOARD continuous monitoring solution is the cornerstone of the continuous monitoring program for dozens of federal contractors throughout the US.

By developing a Comprehensive/Holistic approach to Cybersecurity Defense, our services encompass a multi-layer customizable approach of protection for large organizations, small business owners, or an individual.
Our compliance experts will assist you in meeting and exceeding government compliance rules and regulations.
Cybersecurity for cleared environments is not theoretical. It is operational. It is mission-critical. And it requires more than compliance checklists.
PC-Warriors is led by a former Department of Defense Special Agent who understands national security from the inside — how adversaries think, how investigations unfold, and how government assessors evaluate risk.
This perspective changes everything.
We do not approach cybersecurity as paperwork preparation. We approach it as operational risk management aligned with national defense objectives.
Our experience includes guiding contractors through RMF authorization, DCSA reviews, CMMC readiness, continuous monitoring implementation, and real-world control enforcement — not just policy development.
Because of our investigative background and deep federal expertise, we understand:
When you partner with PC-Warriors, you are not hiring a generic IT consultant. You are working with a mission-focused cybersecurity authority who understands both federal compliance language and technical enforcement at the system level.
In a world where one failed assessment can jeopardize contracts, facility clearances, and reputations, experience matters.
PC-Warriors delivers defensible cybersecurity built to protect contracts, data, and national security.
Due to the lack of cybersecurity awareness, some of our clients make initial contact with us after they have been compromised. When this occurs, there are many critical steps that must be considered. Our first priority is to identify the incident and determine the level of severity and the impact to an organization’s operational status.
The initial objective is to restore the organization to normal operational status. This is accomplished by working closely with the organizations designated staff and disaster recovery procedures.
Should the incident be deemed critical, our team of compliance experts, would perform an in-depth assessment/investigation of the incident and notify the appropriate officials. Any evidence from the attack must also be preserved through proper chain-of-custody procedures to preserve its forensic integrity for legal proceedings.
The attack vector used must be analyzed to prevent future and/or repeated exploits through a careful analysis of injected malware or malicious scripts.
Behind every cyberattack, there is always a human element and motive. We provide a range of cybersecurity training specifically developed for system administrators, executive leadership, and end-users within an organization or entity.
Basic Cybersecurity Awareness training
Technical Best-Practices on maintaining a secure IT Infrastructure
Executive Cybersecurity Top-Down leadership planning
Risk Management Framework (RMF)
Our founder has personally trained enlisted and Officer ranks in all US Military branches for DoD 8570 compliance

For years, PC-Warriors has helped defense contractors:
We do not just “prepare you for the audit.”
We build operationally sound, defensible security programs that withstand scrutiny.

Our team of expert cybersecurity professionals led by Dr. Jose Neto (Former DoD INFOSEC Special Agent) diligently work around the clock staying up to date with the latest vulnerabilities and countermeasures
Recepient of the DSS Director's Coin award for his innovative SSP-Helper Software solution to expedite the processing of C/A packages.